The ability to manage Linux distros via Microsoft Intune has just dropped in this month’s release. With this introduction of the platform, is the ability to enrol a device and manage it for compliance.
If your tenant is flighted, then you will see the new Linux entry on the Devices menu in Endpoint Manager.
Microsoft lists the following as pre-requisites for Linux management:
Devices with:
- Ubuntu Desktop 22.04 or 20.04 LTS
- A GNOME graphical desktop environment
It is recommended to encrypt the Ubuntu device when installing, however for the purposes of the blog post, this has been left decrypted to demonstrate compliance policies.
Install Microsoft Edge for Linux
Micrsoft Edge should be installed on the device and used as the browser to access company resources.
To install Edge, load up the Firefox browser and go to https://www.microsoft.com/en-us/edge and download the Debian/Ubuntu install.
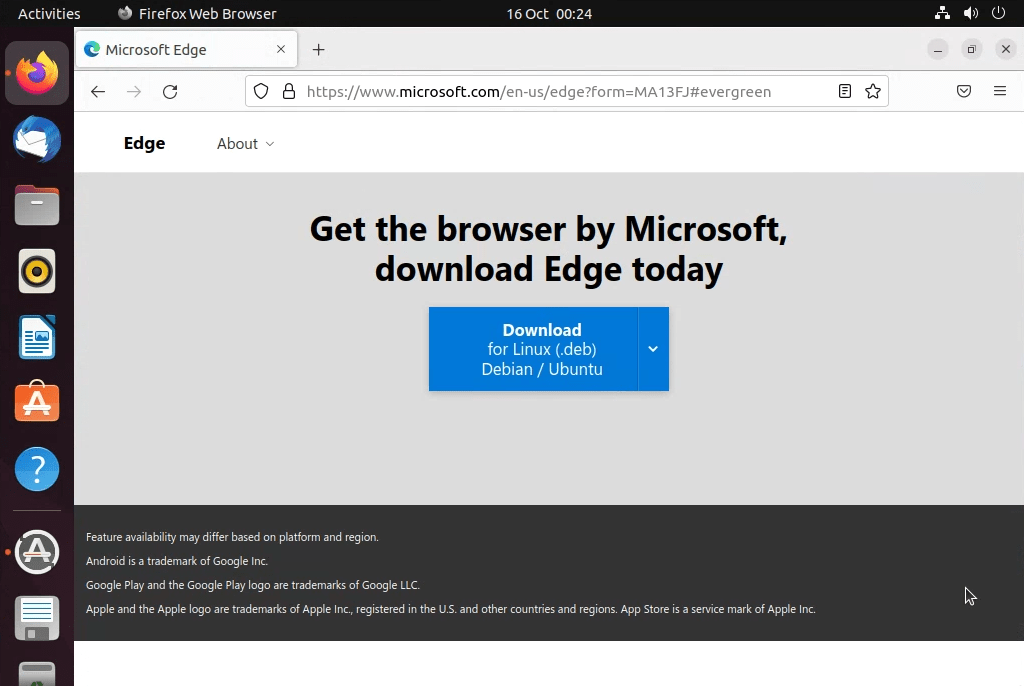
When prompted click the Accept and download button.

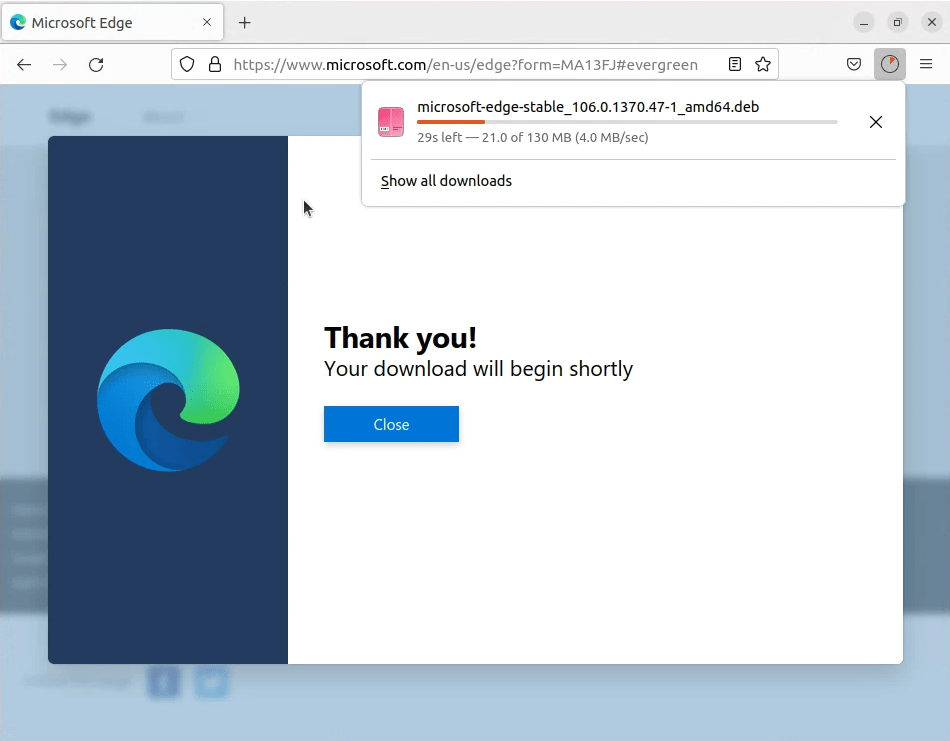
The .deb file will download into the download location.
Double click the file and choose Software install from the Open With… options.
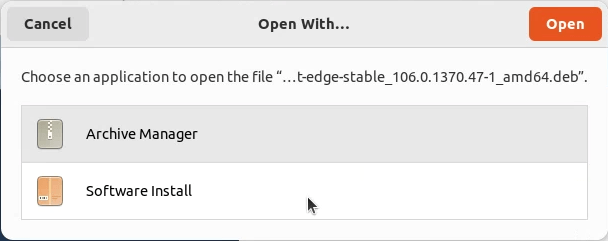
Click Install.

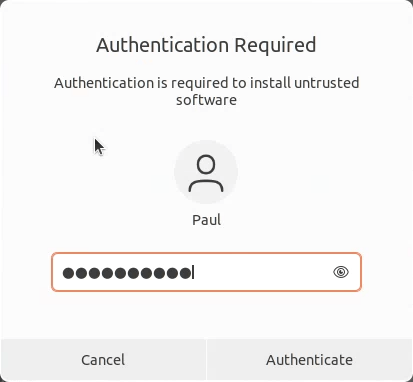
Authentication is required to install the software. Enter a password of an administrator and click Authenticate.
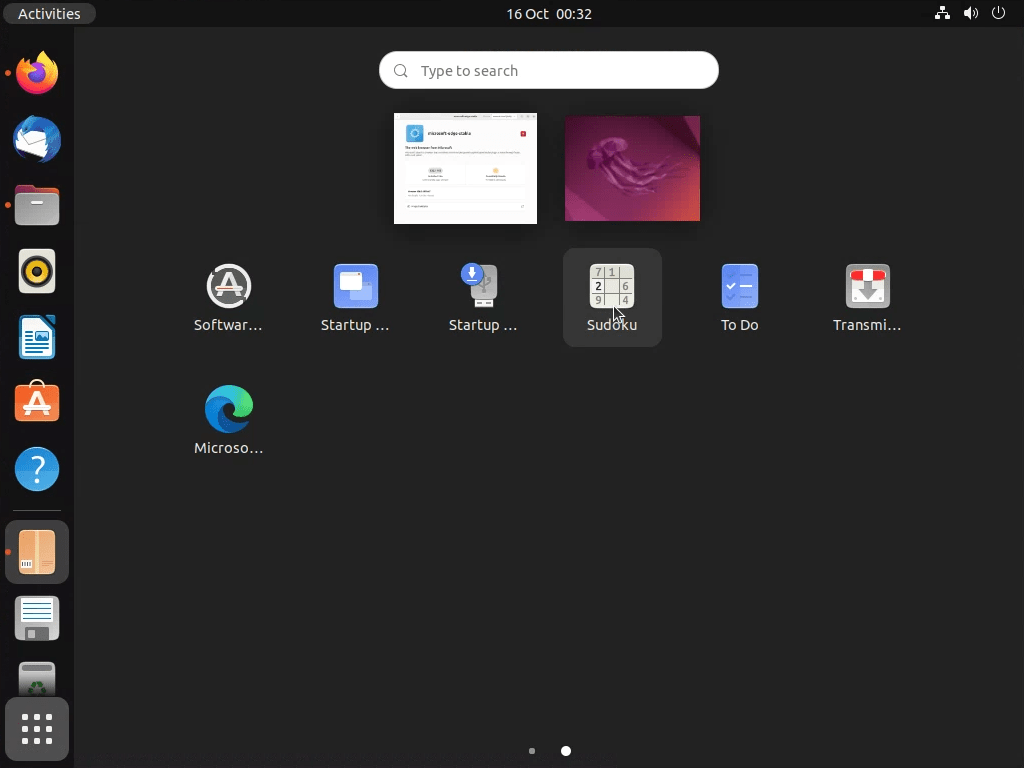
When installed, Microsoft Edge will appear in applications.
Install the Microsoft Intune app
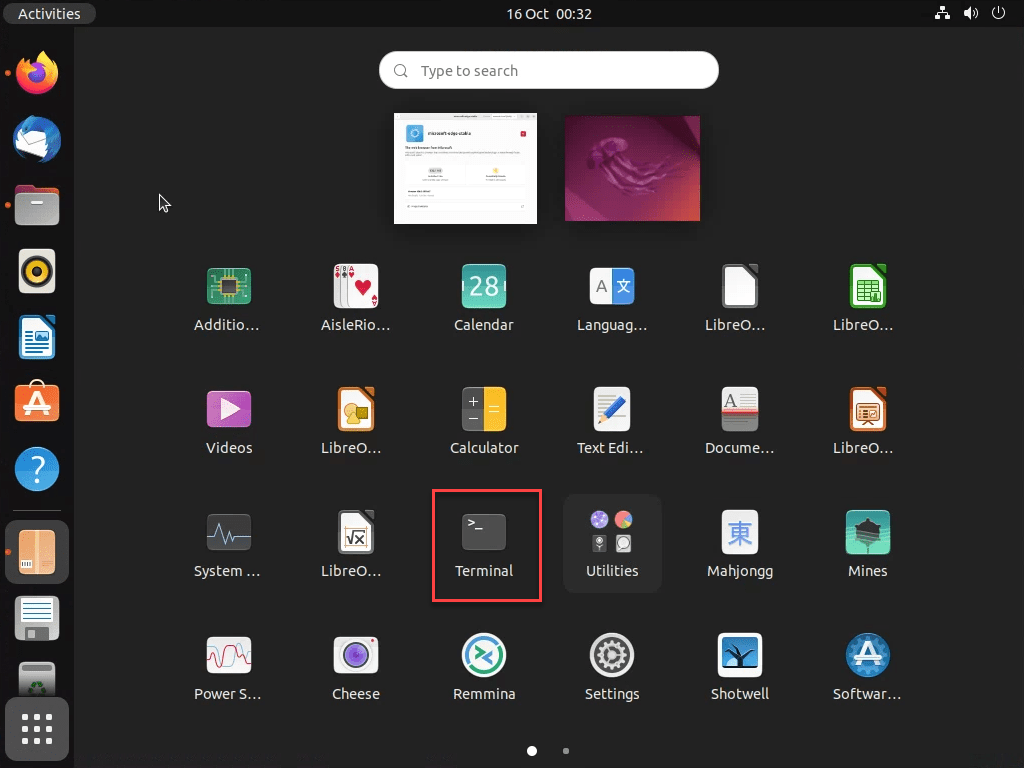
Look for Terminal in applications.
To install the Intune app the following commands are required:
Install Curl:
sudo apt install curl gpg
Install the Microsoft package signing key. There are two different methods depending on the Ubuntu release. Make sure you select the correct release. You can check the release you are running with the following command:
lsb_release -a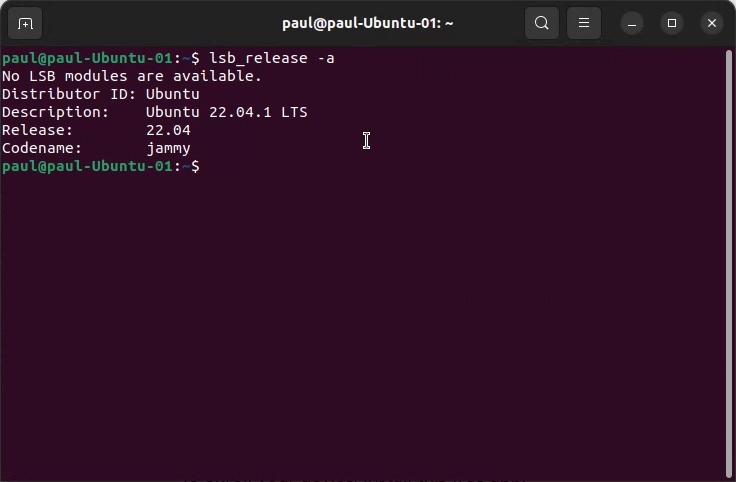
For Ubuntu 20.04:
curl https://packages.microsoft.com/keys/microsoft.asc | gpg --dearmor > microsoft.gpg
sudo install -o root -g root -m 644 microsoft.gpg /usr/share/keyrings/
sudo sh -c 'echo "deb [arch=amd64 signed-by=/usr/share/keyrings/microsoft.gpg] https://packages.microsoft.com/ubuntu/20.04/prod focal main" > /etc/apt/sources.list.d/microsoft-ubuntu-focal-prod.list'
sudo rm microsoft.gpgFor Ubuntu 22.04:
curl https://packages.microsoft.com/keys/microsoft.asc | gpg --dearmor > microsoft.gpg
sudo install -o root -g root -m 644 microsoft.gpg /usr/share/keyrings/
sudo sh -c 'echo "deb [arch=amd64 signed-by=/usr/share/keyrings/microsoft.gpg] https://packages.microsoft.com/ubuntu/22.04/prod jammy main" > /etc/apt/sources.list.d/microsoft-ubuntu-jammy-prod.list'
sudo rm microsoft.gpgInstall the Microsoft Intune app
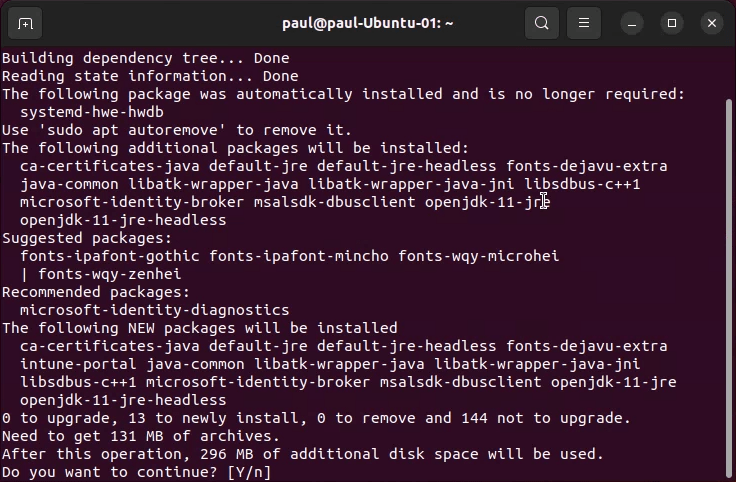
To install the app run the following commands:
sudo apt update
sudo apt install intune-portalOnce the install is completed, reboot the device.


The Micrsoft Intune app will appear in the list of applications. Double click to run the app.
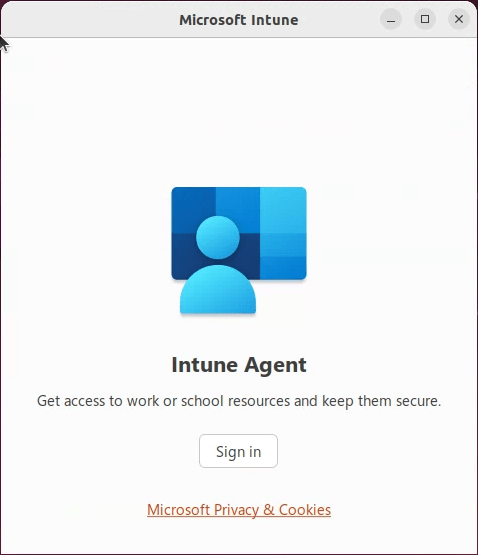
You will be asked to Sign in to the Intune agent. Click the button to continue.
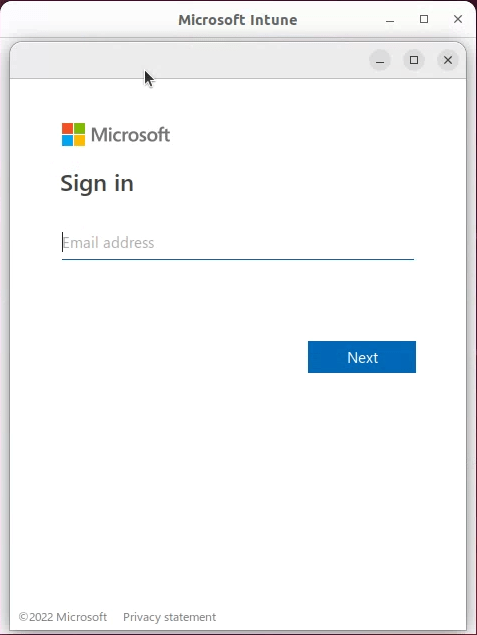
Enter the username for your work or school account.
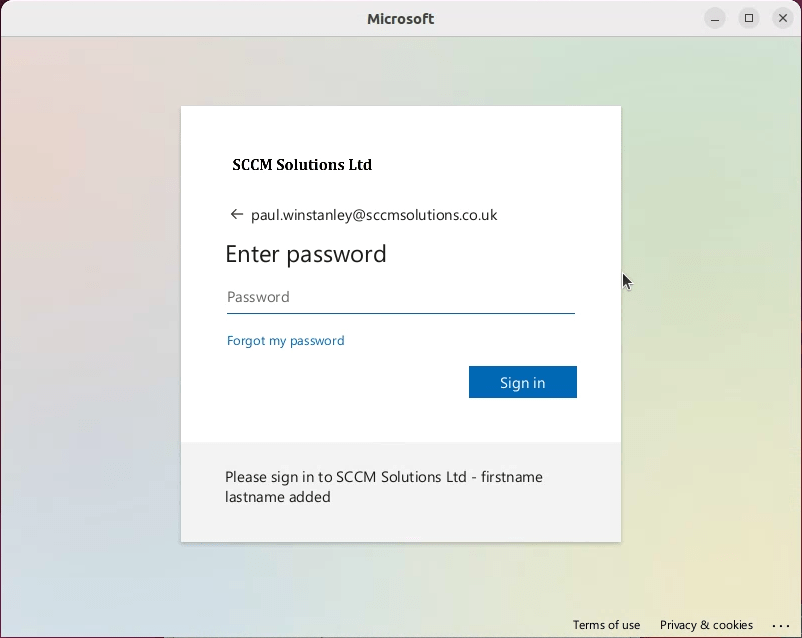
When prompted enter your password.
You will now be asked to register the device. Click the Register button.

if you have MFA enabled against your account, you will be prompted to Approve sign in request.

Click the Begin button to start the device registration process.

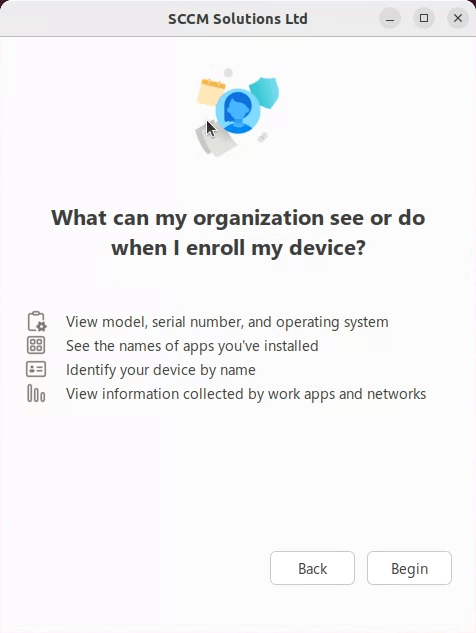
You will be informed of what the organization can see when the device is enrolled. Click Begin to continue.
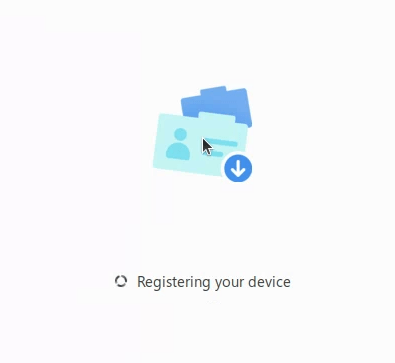
The device will register with the organization.
Once registered, the device will automatically check for compliance.
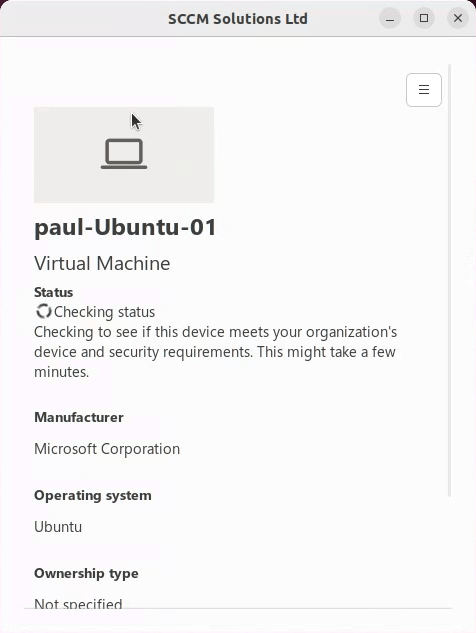
At this stage, I didn’t have any compliance policies set therefore the device was marked as Compliant.
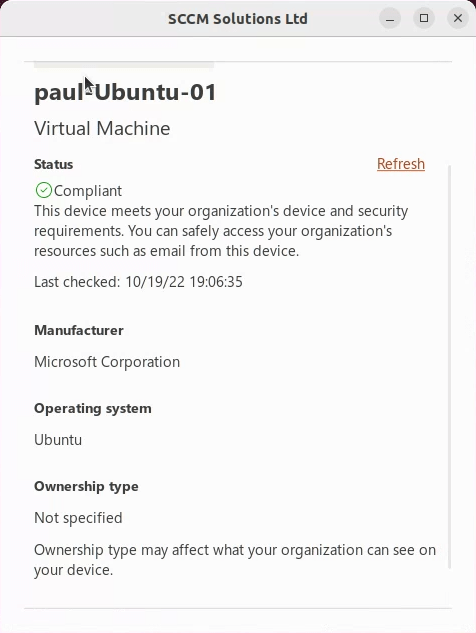
The device will appear in the Intune portal under the Linux devices node. Note that the device comes in as Corporate ownership.

Set up a Linux Compliance Policy
Now we are going to set up a compliance policy for the Linux device and block access to Office 365 if not compliant.
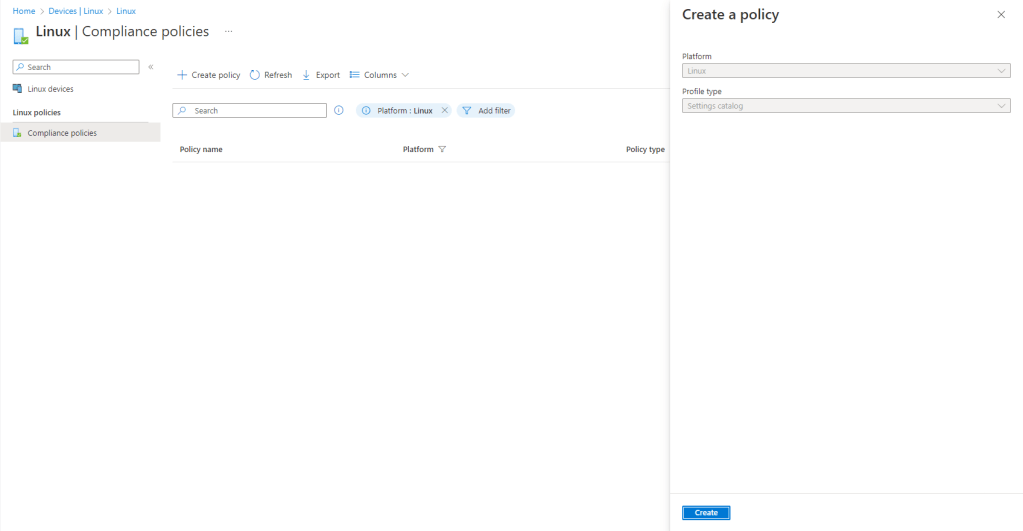
In the Endpoint Manager portal, navigate to Devices\Linux\Compliance policies. Click Create policy. The profile type will automatically be set to Settings catalog and the platform will be Linux. Click Create.
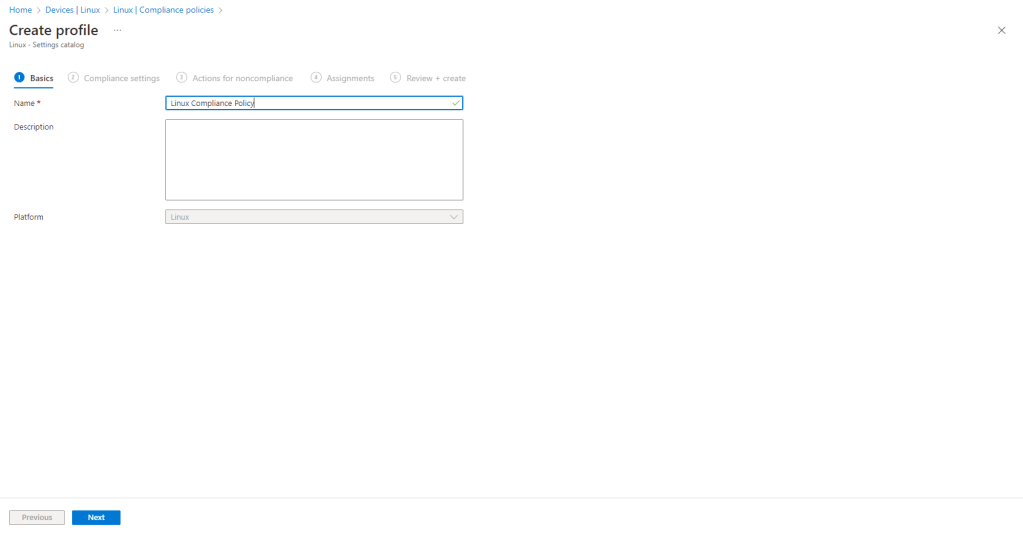
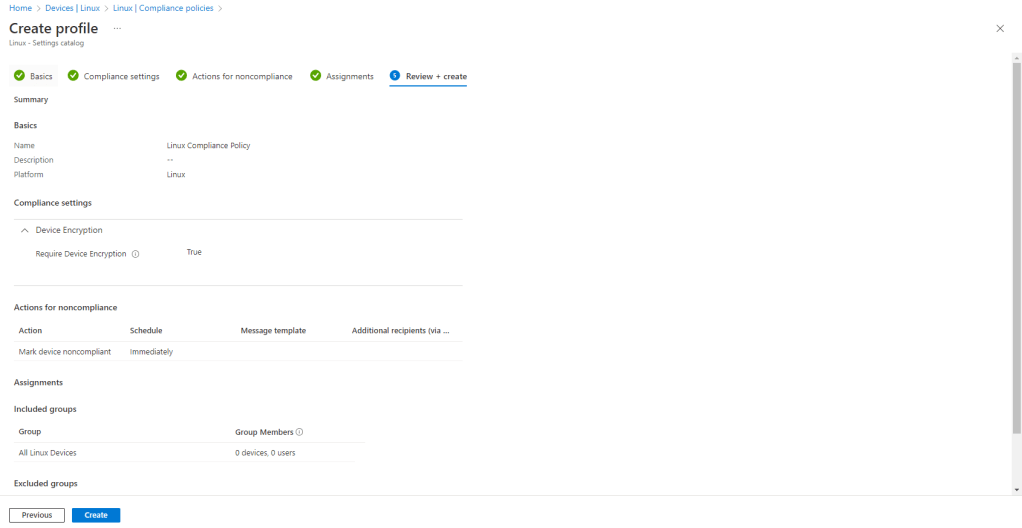
Enter a Name for the policy and click Next.
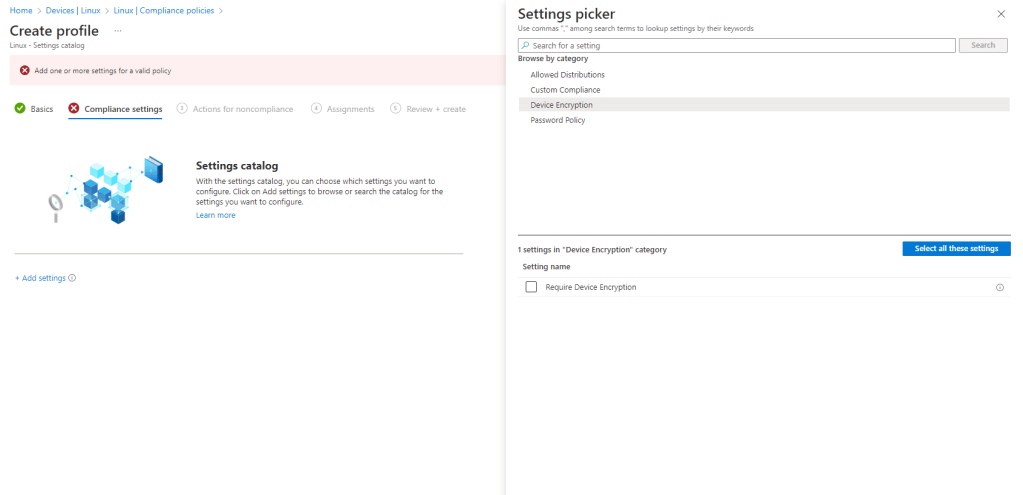
Click the + Add settings option and you have different settings to choose from in the Settings picker. I have chosen to check for encryption. Under Device Encryption click Require Device Encryption.
Flip the Require Device Encryption toggle to True and click Next.

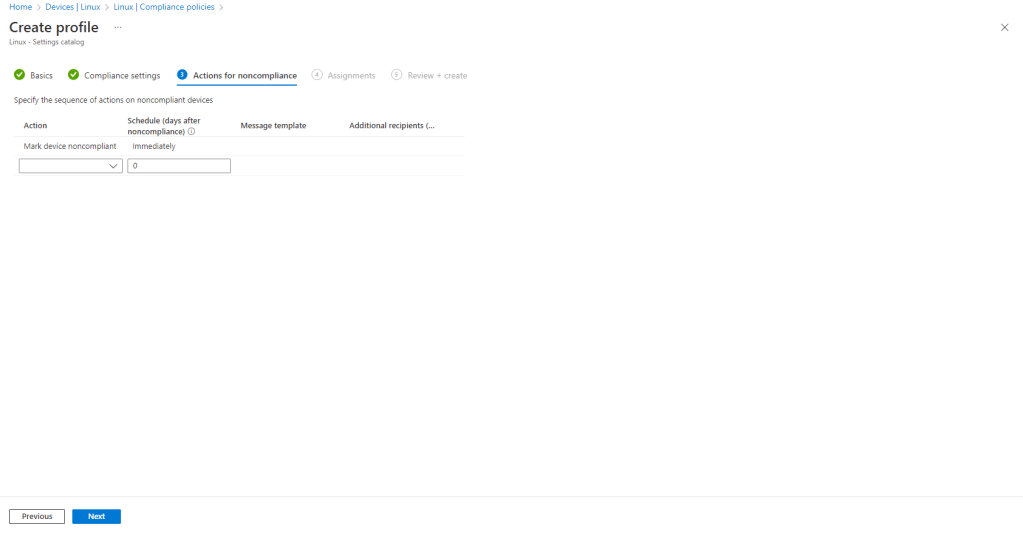
I have set the Action for noncompliance to mark the device as non-compliant immediately. Click Next.
Assign the policy accordingly. I have created a dynamic group of devices with OS type set to Linux and used this for targeting. Click Next.

Review and Create the policy.
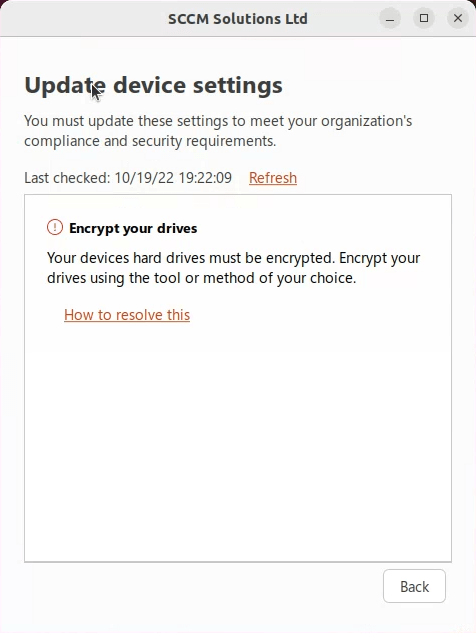
Refreshing the Intune app on the device shows that this is now marked as Not compliant.

Clicking the View issues button confirms this is due to the drive not being encrypted.
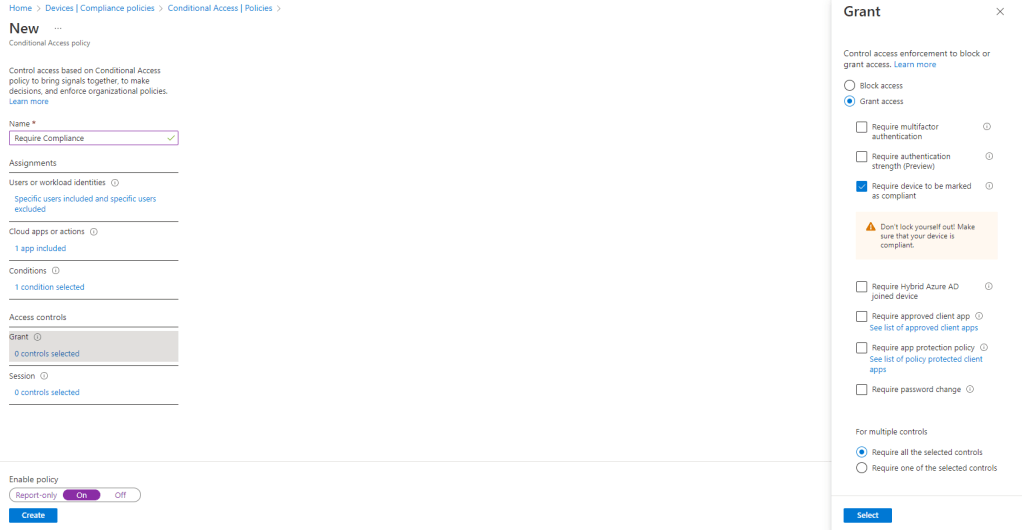
In my conditional access rules, I am able to select Linux as the platform.
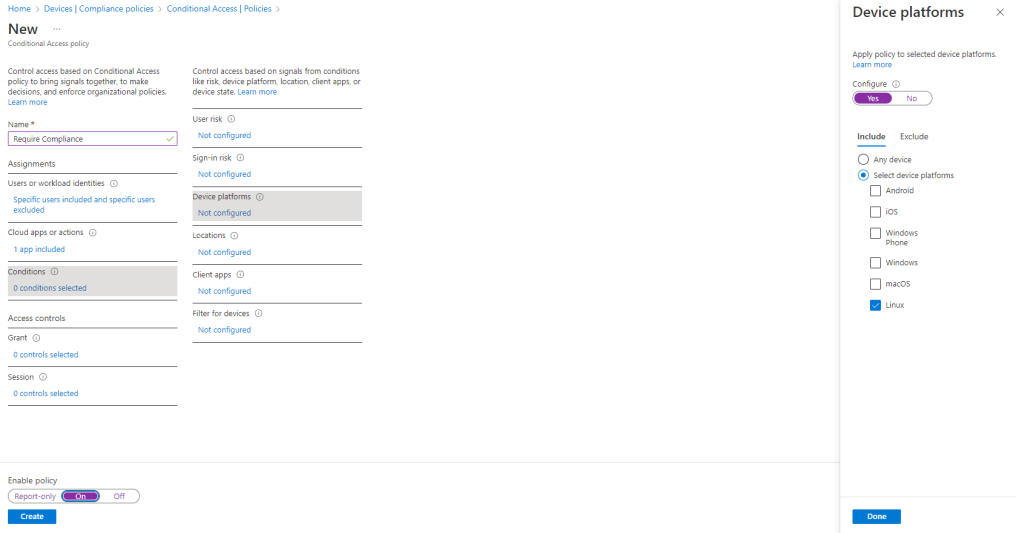
and I can ensure that the device must be marked as compliant for me to be able to use the cloud app, in this case Office.
When attempting to use Office.com on the device in Microsoft Edge I get the standard Get access to this resource message which states that the device is not compliant.
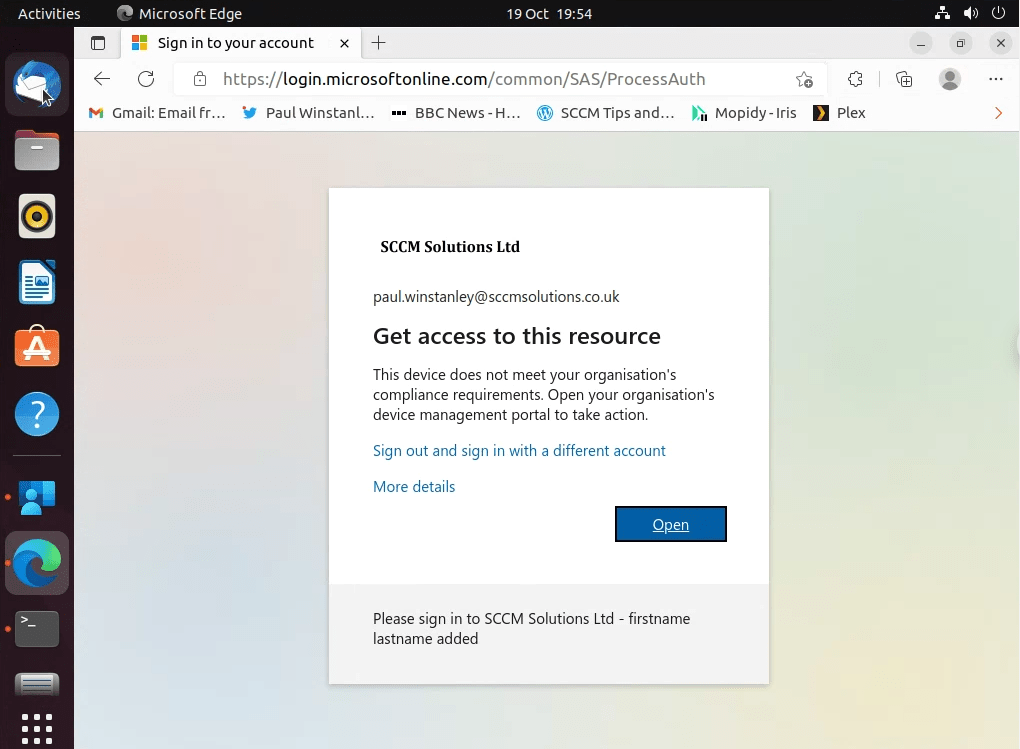
If I attempt to get around this, and use Firefox, I get the following message. Which is a great way to force me into ensuring that I need to get this device compliant to be able to access the company resources.

This is a great start into Linux management via Microsoft Intune and I’m looking forward to seeing what features Microsoft come up with in the near future.
Two times For Ubuntu 20.04 repeated.
Also have you tried password compliance policy? Even if existing password matches the criteria, the device still shows as non-compliant..even after changing password to match policy, the device doesn’t change to complaint.
Thanks I’ve updated the heading. Cheers Paul
For password policy to work follow “”like below. Basically, Intune checks pam.pwquality configuration for enforcement w.r.t Password policy.
install the following by running the command: sudo apt install libpam-pwquality
Next, check that pam-pwquality line in /etc/pam.d/common-password contains at least the required settings set in Intune.
pam_pwquality.so retry=3 dcredit=-1 ocredit=-1 ucredit=-1 lcredit=-1 minlen=8
Does anyone know why GNOME is only supported DE? Anyone tried with a different DE – e.g. KDE/Plasma?
@rudiik,
The portal needs window manager running under gdm. I suspect this is because the intune brokee uses Dbus for ipc message passing and other DIsplay manager doesn’t support. This is probably a lightweight dbus library though
Your commands would be easier with a sudoers policy (removed post-configuration) for NOPASSWD:(ALL), turning them into a script, or by piping a loop in the commands… less re-entry of credentials 🙂
Hey Nick, those commands come straight from Microsoft. I’d be interested to see how you format them. Cheers Paul
-Writing this quickly, please forgive any minor errors-
The easiest temp fix is to allow noauth sudo or script it (all commands inline, sudo +x the .sh file).
No auth: modify /etc/sudoers to reflect the following name, modifying username; near the bottom of the file then remove changes when complete for security:
%username% ALL = ALL(ALL) NOPASSWD:ALL
That option will allow sudo without constant re-authentication. Use “sudo nano -w /etc/sudoers” or “sudo vi /etc/sudoers” to make changes (same goes for a Mac- off topic, but useful).
Otherwise, compile all lines into one file similar to this example using nano/vi/whichever editor that you choose (does not work with all configs, still useful) by saving as something like “enableintune.sh” followed by the command “sudo chmod +x enableintube.sh” to make the file executable easily. Once saved, “sudo ./enableintune.sh” to kick it off:
“#!/bin/bash
apt-get update
apt install curl gpg
curl https://packages.microsoft.com/keys/microsoft.asc | gpg –dearmor > microsoft.gpg
install -o root -g root -m 644 microsoft.gpg /usr/share/keyrings/
apt-get update
…etc…”
If you choose the first, obviously return the file /etc/sudoers to its original state once complete. As a safety measure, comment out the permanent sudoers rule for the authid with a “#” and write the temporary.
Either should save a ton of time of re-entering passwords 🙂
All the best my friend, I hope all is well!
I close the Intune Agent window and the config get lost (I need to re-register the device by running the Intune agent, iteractively). Is this a known issue? Mine is Ubuntu 22 Azure VM. Thanks!
I haven’t seen this happen tbh, David.I have had the Intune agent crashing constantly recently though.
It’s being reported here, also: Microsoft Intune agent on Linux – Microsoft Community Hub. Seems a known issue. Do you know where can I find the local Intune-Portal agent logs on my Ubuntu VM? Those should be handy to debug further.. Thanks for the quick reply!
Ah, I have seen the resign in behaviour for sure recently. Not sure where the logs are stored apologies.
“First steps into Linux management” – Still waiting on Intune to continue with step 2, three years later… 😅