In the third entry in the Keep it Simple with Intune series, I show you how to enforce BitLocker disk encryption on your Windows 10 device and store the recovery key in Azure AD.
Encrypting the device via Intune with BitLocker is very simple to set up. As with our start menu from #2 in the series, you will need to configure a device configuration profile in the Azure Portal and assign this to your devices.
In the portal, navigate to Intune>Device Configuration>Profiles. Click Create Profile.
Enter a Name for the profile, a Description choose Windows 10 and later for the Platform and select Endpoint Protection for the Profile type. Scroll down the Endpoint Protection blade and select Windows Encryption.

From here you can select the BitLocker encryption settings you wish to applying to your devices. Encrypt devices needs to be set to Require. I recommend that XTS-AES 265-bit is set for the operating system drive.

A choice of start up type is available, TPM only, TPM + PIN, for example.
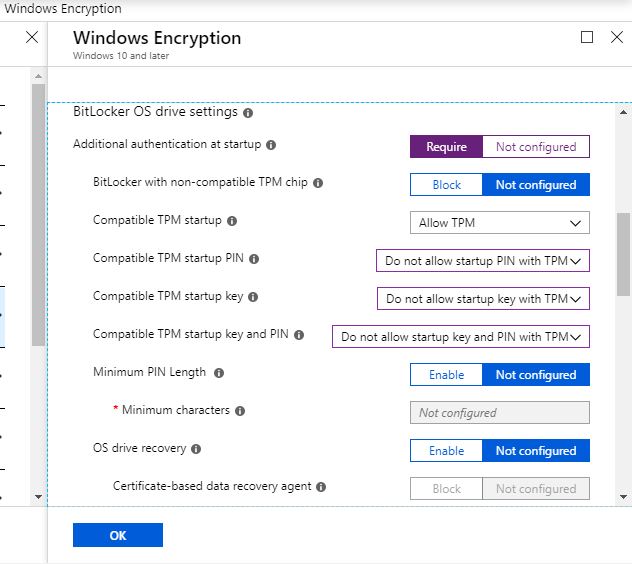
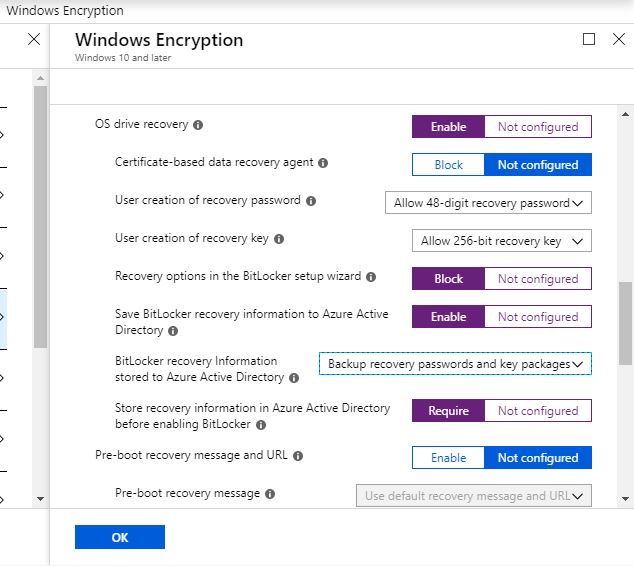
Also the ability to block user choice on recovery key save options, forcing the key to be saved into Azure AD.
With the relevant settings configured click OK, OK and Save.
After creating the profile, assign this to the relevant set of devices.

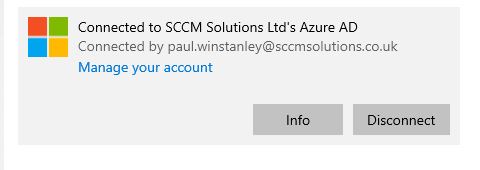
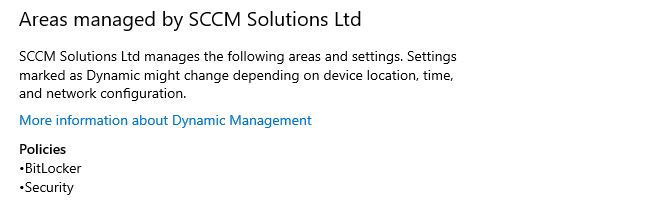
When your device syncs you can see that the BitLocker policy has been applied under Settings>Accounts>Access work or school on the Windows 10 device and by clicking the connected accounts details and selecting Info.
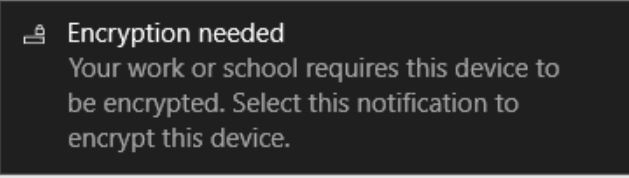
The end user will be notified that Encryption is needed on the device.
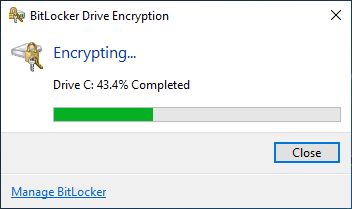
The user can choose to encrypt used space or the entire drive.
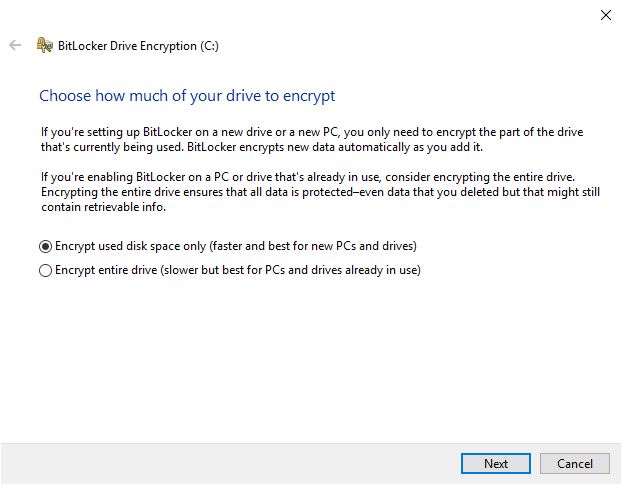
The options which appear in the wizard are determined by the configuration of the BitLocker profile. For my settings, I have not given the user an option of where to save the recovery key, opting instead to save this immediately into Azure AD.
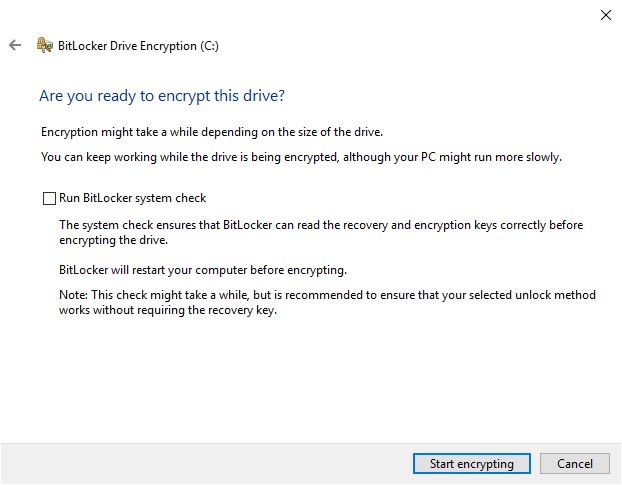
The user is given the choice of running a BitLocker system check before beginning the encryption.

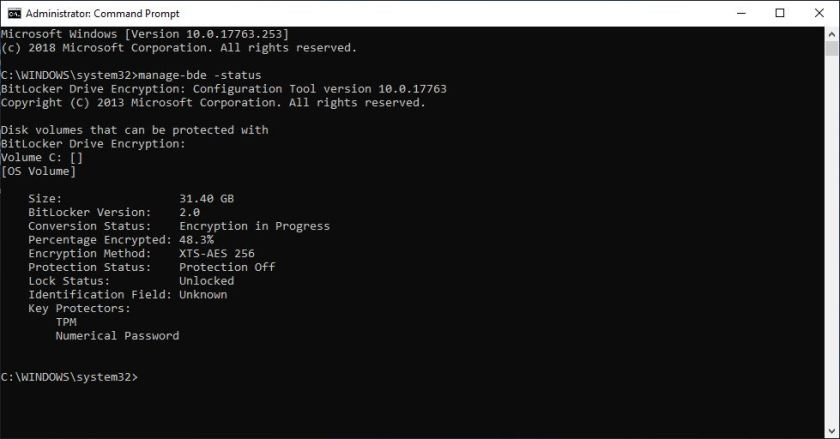
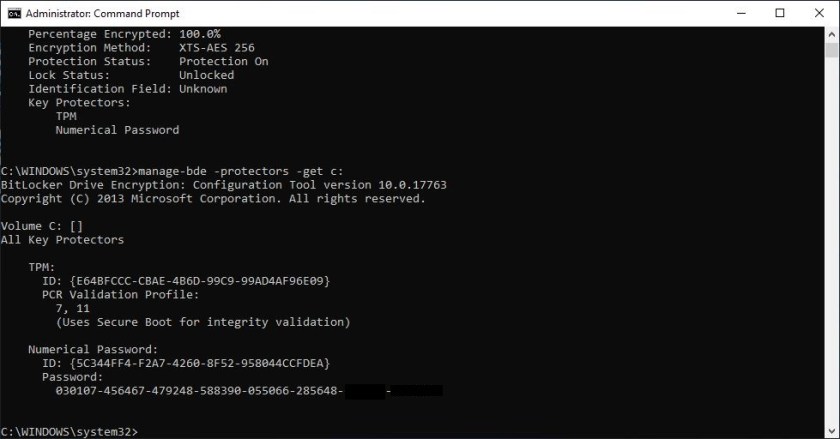
By running manage-bde -status I can see that the XTS-AES 256 algorithm I selected in the profile is being enforced.
and by issuing the command manage-bde -protectors -get c: I can take a look at the recovery key which, if this has all worked, should be stored in the Azure AD.
A user is able to get the BitLocker recovery key associated with their device when going to the address https://account.activedirectory.windowsazure.com/r/#/profile.

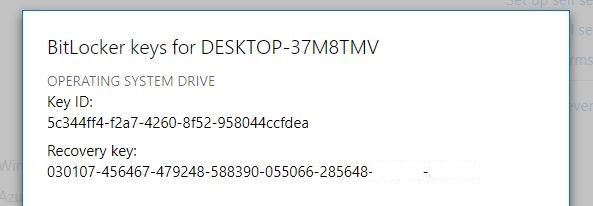
Admins can check the recovery key information in the Azure Portal by navigating to Azure Active Directory>Devices and selecting the Device.

Look out for more in the Keep it Simple with Intune series soon.
Hi SCCMentor!
Thanks for taking your time to write up this great article. Easy to follow and implement.
I’m planning the migration of on-premise AD joined Win 10 machines which are already Bitlocker encrypted to modern management using AAD and Intune.
Would you know if I need to decrypt and re-encrypt using this Intune policy? Or is it possible to leave the Win10 machine encrypted and ensure the recovery PIN is re-uploaded to AAD?
Thanks in advance,
Richard
Richard, as far as I am aware the registration of the key will not happen automatically. I could be wrong however. If not then I suggest taking a look at implementing a script to kick the storage into AAD into life. Take a look here for a suggestion https://social.technet.microsoft.com/Forums/en-US/22c95a67-1ec5-4874-9140-c5facd29cfd8/register-bitlocker-recovery-key-to-azure-ad. Cheers Paul
Hi Paul!
Thanks for the quick reply. Thanks for sharing and I will let you know what the outcome is!
Kind regards,
Richard
Awesome cheers Richard.
Has the workflow for this changed? I’m seeing the user get the prompt about third party encryption, but now when they click the Yes button, it brings up the Device Encryption section of the Modern Settings app instead of launching the bitlocker wizard. From there, when the user clicks “Turn on” it says “Something went wrong. Try again later”. Going into the Bitlocker control panel area and turning bitlocker on there actually launches the bitlocker wizard and prompts the user to set their pin.